Does the IRS audit people on Social Security?
 Emma Jordan
Emma Jordan 
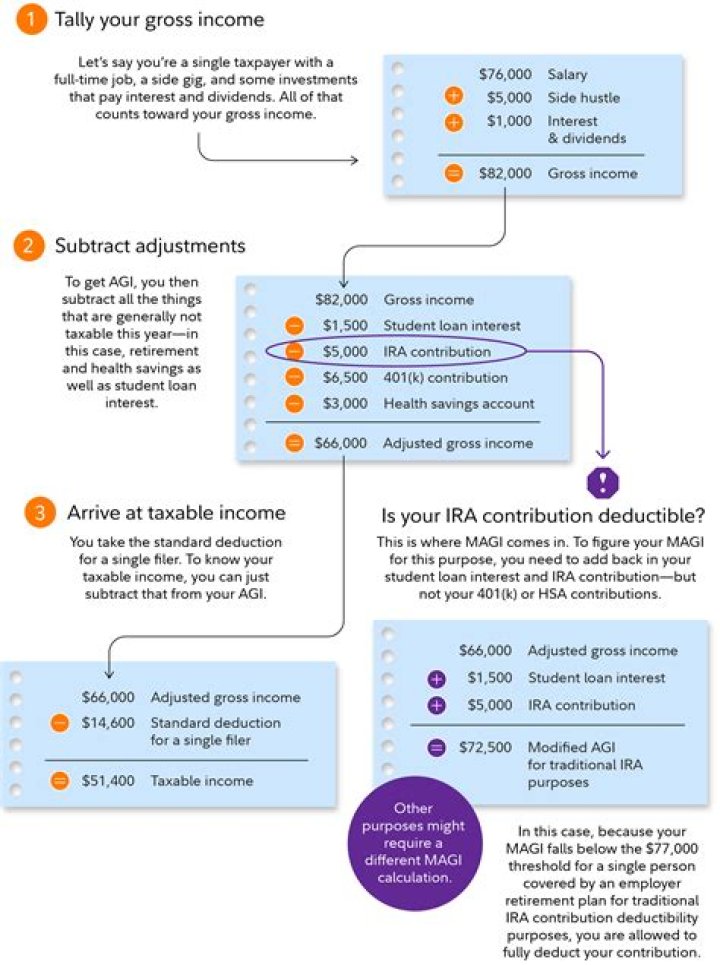
Failing to report taxable income from wages, dividends, pensions, IRA distributions, Social Security benefits and other sources will almost certainly draw unwanted attention from the IRS. The IRS gets copies of all the 1099s and W-2s you receive.
What happens if you don’t do an audit?
Here’s what happens if you ignore an office audit: You may have avoided the meeting, but you’ll pay for it later in taxes, penalties, and interest. The IRS will change your return, send a 90-day letter, and eventually start collecting on your tax bill. You’ll also waive your appeal rights within the IRS.
Which is an example of Mam without enrollment?
MAM protects an organization’s data within an application. With MAM without enrollment (MAM-WE), a work or school-related app that contains sensitive data can be managed on almost any device, including personal devices in bring-your-own-device (BYOD) scenarios. Many productivity apps, such as the Microsoft Office apps, can be managed by Intune MAM.
Can a MAM policy be applied to a BYOD device?
If you apply a MAM policy to the user without setting the device state, the user will get the MAM policy on both the BYOD device and the Intune-managed device. You can also apply a MAM policy based on the managed state. So when you create an app protection policy, next to Target to all app types, you’d select No.
Can a Microsoft Office app be managed by MAM without enrollment?
With MAM without enrollment (MAM-WE), a work or school-related app that contains sensitive data can be managed on almost any device, including personal devices in bring-your-own-device (BYOD) scenarios. Many productivity apps, such as the Microsoft Office apps, can be managed by Intune MAM.
When to use mam-we for personal use?
When combined with app protection policies, you can protect data within an app. MAM-WE is commonly used for personal or bring your own devices (BYOD). Or, used for managed devices that need extra security.