How can information security be improved in an organization?
 Emily Baldwin
Emily Baldwin 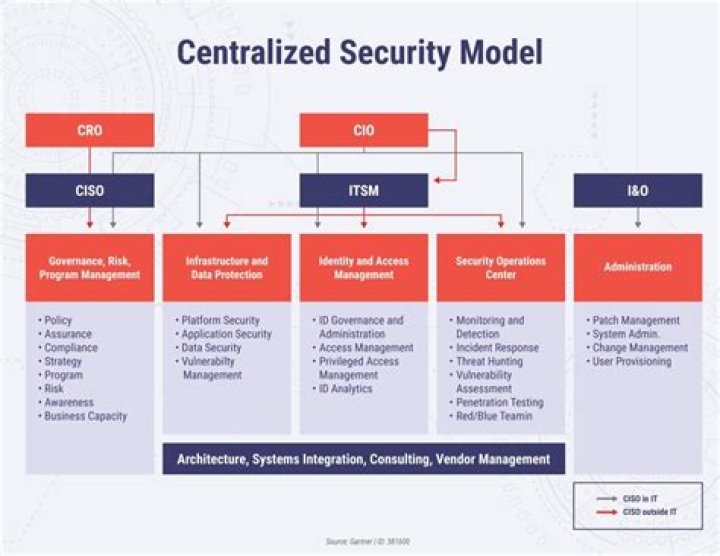
In this post, we outline five things you can do to improve the way you approach information security.
- Support cyber security staff.
- Conduct annual staff awareness training.
- Prioritise risk assessments.
- Regularly review policies and procedures.
- Assess and improve.
What is the need for an organization to follow information security?
Why is information security important? Without information security, an organization’s information assets, including any intellectual property, are susceptible to compromise or theft. As a result, consumer and shareholder confidence and reputation suffer potentially to the point of ruining the company altogether.
What is organization security?
Security is to combine systems, operations and internal controls to ensure integrity and confidentiality of data and operation procedures in an organization.
How do you develop information security strategy?
Build an Information Security Strategy
- Assess security requirements. Define the business and security goals of your security program and determine the organization’s security pressure risk overview.
- Build a gap initiative strategy.
- Prioritize initiatives and build roadmap.
- Execute and maintain.
How do you manage information security?
Continuous improvement in information security
- Plan. Identify the problems and collect useful information to evaluate security risk.
- Do. Implement the devised security policies and procedures.
- Check. Monitor the effectiveness of ISMS policies and controls.
- Act. Focus on continuous improvement.
What are the 3 ways Security is provided?
There are three main types of IT security controls including technical, administrative, and physical. The primary goal for implementing a security control can be preventative, detective, corrective, compensatory, or act as a deterrent.
What is an IT security strategy?
From Wikipedia, the free encyclopedia. A Security Strategy is a document prepared periodically which outlines the major security concerns of a country or organisation and outlines plans to deal with them.
What are the security strategies?
Here are the 4 cyber security strategies every financial services company needs to be using to secure its business across current and emerging threats:
- Put Cyber Security First.
- Prioritize Threats.
- Be Proactive.
- Get Real.
What is the purpose of information security management?
The purpose of information security management is to ensure business continuity and reduce business damage by preventing and minimising the impact of security incidents.
What are types of security?
There are four main types of security: debt securities, equity securities, derivative securities, and hybrid securities, which are a combination of debt and equity.
What are the steps in security awareness?
8 Steps to Implement a Cyber Security Awareness Training Program
- Get Buy-in From Company Leadership.
- Perform Risk Assessment Reports.
- Provide Interactive Training Courses.
- Schedule Regular Testing.
- Compile Test Results and Make Improvements.
- Implement and Enforce New Policies.
- Retrain Employees Regularly.
- Be Consistent.
How do you demonstrate security awareness?
9 Ways to Create a Security Awareness Program People Won’t Hate
- Establish advocates and achieve buy-in.
- Narrow your focus.
- Connect to real-life attacks.
- Make it about them.
- Execute mock attacks to establish effectiveness.
- Raise their emotional commitment.
- Be flexible.
- Reward the top dogs.
How do you understand information security management?
Information security management describes the set of policies and procedural controls that IT and business organizations implement to secure their informational assets against threats and vulnerabilities.
Below are six best practices you can use to improve your organization’s security posture.
- Conduct a cybersecurity risk assessment.
- Prioritize risk.
- Track security metrics.
- Implement automated cybersecurity solutions.
- Educate your employees.
- Create an incident response plan.
Why is information security important? Without information security, an organization’s information assets, including any intellectual property, are susceptible to compromise or theft.
We define organizational security as a sustained, appropriate level of security in team communication and information management practices. When more than one person works together to achieve a goal, they need to be able to communicate and manage information to get things done.
How do you develop an information security strategy?
How can I improve system security?
9 Ways to Improve the Security of Your Home Computer
- Connect to a Secure Network.
- Enable and Configure a Firewall.
- Install and Use Antivirus and Anti-spyware Software.
- Remove Unnecessary Programs.
- Modify Unnecessary Default Features.
- Operate Under the Principle of Least Privilege.
- Secure Your Web Browser.
What are the four requirements of security implementation?
Summarizing, the security requirements must cover areas such as:
- Authentication and password management.
- Authorization and role management.
- Audit logging and analysis.
- Network and data security.
- Code integrity and validation testing.
- Cryptography and key management.
- Data validation and sanitization.
What are the 4 types of IT security?
Types of IT security
- Network security. Network security is used to prevent unauthorized or malicious users from getting inside your network.
- Internet security.
- Endpoint security.
- Cloud security.
- Application security.
How do you structure an information security organization?
Ultimately, there are many ways to structure your information security organization. Budgetary constraints, senior leadership objectives and mandates will dictate your functional needs which will then influence your organizational structure. FINAL REMARKS Ultimately, different organizational models work across industries, and competing
What is an information security and risk management strategy?
An information security and risk management (ISRM) strategy provides an organization with a road map for information and information infrastructure protection with goals and objectives that ensure capabilities provided are aligned to business goals and the organization’s risk profile.
Why is ISACA important for information security and risk management?
Why ISACA? An information security and risk management (ISRM) strategy provides an organization with a road map for information and information infrastructure protection with goals and objectives that ensure capabilities provided are aligned to business goals and the organization’s risk profile.
How to build the most effective information security framework?
Nessus Pro, the industry-leading vulnerability assessment solution, is the ideal complement to many information security frameworks, including custom approaches. Alternatively, we offer solutions to help observe specific protocols, such as Tenable.sc’s support for ISO 27001 compliance and Tenable.io’s PCI ASV variant .