How do you evaluate cyber security?
 Emily Baldwin
Emily Baldwin 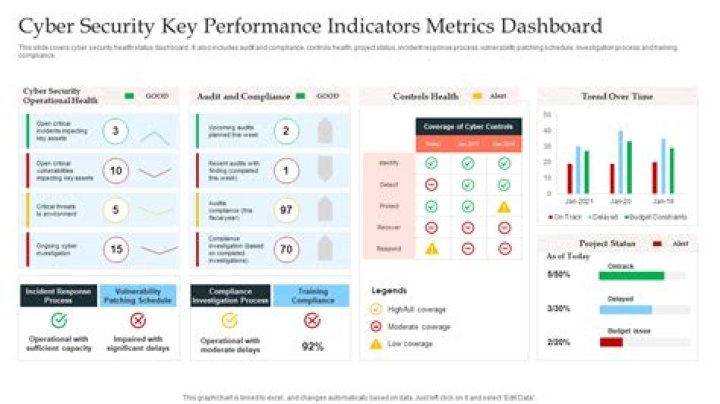
How to Evaluate Cybersecurity Risk Assessment Services
- Identify and prioritize valuable information.
- Determine the threat.
- Determine the Vulnerabilities.
- Analyse controls and execute new ones.
- Estimate the possibility of various scenarios on a yearly basis.
What is an information security risk assessment?
A security risk assessment identifies, assesses, and implements key security controls in applications. It also focuses on preventing application security defects and vulnerabilities. Thus, conducting an assessment is an integral part of an organization’s risk management process.
How do you conduct a security assessment?
The steps below will help an organization build an effective risk assessment framework.
- Define the requirements.
- Identify risks.
- Analyze risks.
- Evaluate risks.
- List risk treatment options.
- Conduct regular visits.
How do you determine security risk?
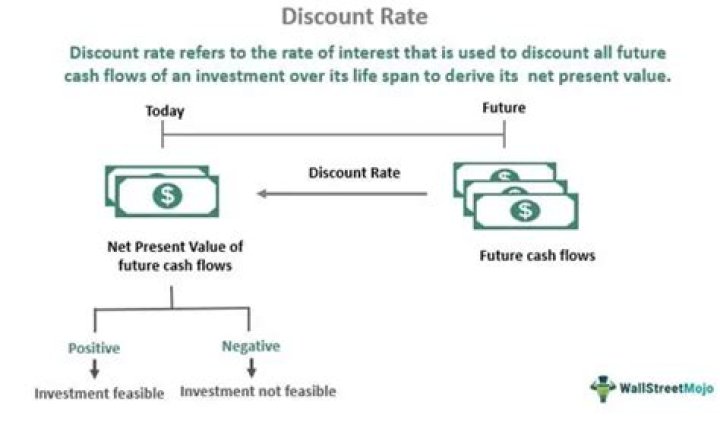
Risk is calculated by multiplying the threat likelihood value by the impact value, and the risks are categorized as high, medium or low based on the result.
What are the security principles?
The Principles of Security can be classified as follows:
- Confidentiality: The degree of confidentiality determines the secrecy of the information.
- Authentication: Authentication is the mechanism to identify the user or system or the entity.
- Integrity:
- Non-Repudiation:
- Access control:
- Availability:
What is security assessment tools?
Organisations are looking for a way to check their security status quickly and simply. They want insight into their vulnerabilities, based on data from the company infrastructure and Office 365.
Why is security assessment important?
Security assessments enable your IT team to identify areas of weakness and opportunitiesfor growth in security protection. Understanding where current vulnerabilities exist, and which are priority, allows your IT team to make better informed decisions about future security expenses.
What are examples of security hazards?
Some common safety concerns include falls, trips, fire hazards, road accidents, bumps and collisions. Moreover, physical hazards, such as insufficient lighting, noise and inappropriate levels of temperature, ventilation and humidity, can put your security guards’ health and safety at risk.
What is the main aim of security?
All information security measures try to address at least one of three goals: Protect the confidentiality of data. Preserve the integrity of data. Promote the availability of data for authorized use.
What are the primary goals of security?
Three primary goals of information security are preventing the loss of availability, the loss of integrity, and the loss of confidentiality for systems and data. Most security practices and controls can be traced back to preventing losses in one or more of these areas.
What are the types of security attacks?
8 types of security attacks and how to prevent them
- Malware. Malicious software – ‘malware’ – infects devices without users realizing it’s there.
- Drive-by downloads.
- Phishing.
- Brute-force attacks.
- SQL Injections.
- Man-In-The-Middle (MITM) attacks.
- Denial-of-Service (DoS) attacks.
- Cross-Site Scripting (XSS)
Which are OS assessment tools?
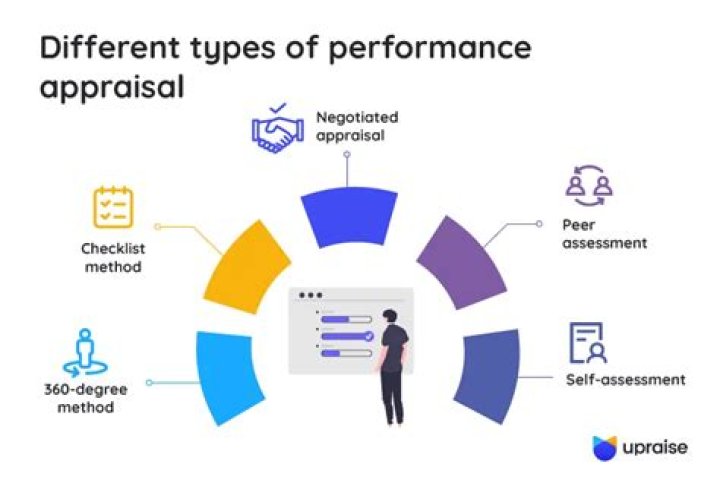
Assessment tools aid in assessing and evaluating student learning and can provide different options to assess students beyond the traditional exam. Several tools are available including grading rubrics , Canvas Assignments , plagiarism detection, self-assessment, and peer assessment, surveys, and classroom polling.
What is an automated assessment tool?
What is the Automation Assessment Tool? A series of spreadsheets with an accompanying manual that is used to guide the collection of data that allows a team of process owners to determine if automation is necessary to meet customer demand.
What is security checklist?
Filters. A checklist developed by security experts using questions dealing with a number of security issues.
When should a security assessment be conducted?
Security risk assessment should be a continuous activity. A comprehensive enterprise security risk assessment should be conducted at least once every two years to explore the risks associated with the organization’s information systems.
What are the 3 D’s of security?
deterrence, denial and detection
Home security strategies can be broadly classified into three categories, often referred to as the three “Ds” of home security. These are deterrence, denial and detection.
What are examples of physical security?
Physical security involves the use of multiple layers of interdependent systems that can include CCTV surveillance, security guards, protective barriers, locks, access control, perimeter intrusion detection, deterrent systems, fire protection, and other systems designed to protect persons and property.
What are the five goals of security?
The five security goals are confidentiality, availability, integrity, accountability, and assurance.
- Step #1: Identify and document asset vulnerabilities.
- Step #2: Identify and document internal and external threats.
- Step #3: Assess your vulnerabilities.
- Step #4: Identify potential business impacts and likelihoods.
- Step #5: Identify and prioritize your risk responses.
What is a good way to evaluate information security risk?
How to Conduct an IT Security Risk Assessment: Key Steps
- Identify and catalog your information assets.
- Identify threats.
- Identify vulnerabilities.
- Analyze internal controls.
- Determine the likelihood that an incident will occur.
- Assess the impact a threat would have.
- Prioritize the risks to your information security.
How do you write a security evaluation?
Tips for Creating a Strong Cybersecurity Assessment Report
- Analyze the data collected during the assessment to identify relevant issues.
- Prioritize your risks and observations; formulate remediation steps.
- Document the assessment methodology and scope.
- Describe your prioritized findings and recommendations.
What is risk security?
In cybersecurity, risk is the potential for loss, damage or destruction of assets or data. Threat is a negative event, such as the exploit of a vulnerability.
The fundamental principles (tenets) of information security are confidentiality, integrity, and availability. Every element of an information security program (and every security control put in place by an entity) should be designed to achieve one or more of these principles. Together, they are called the CIA Triad.