What causes frequent account lockout?
 Sophia Bowman
Sophia Bowman 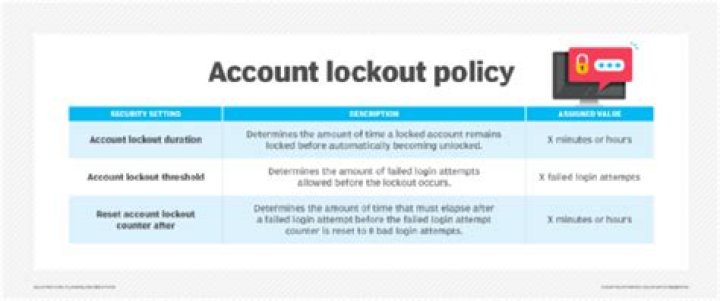
The common causes for account lockouts are: End-user mistake (typing a wrong username or password) Programs with cached credentials or active threads that retain old credentials. Service accounts passwords cached by the service control manager.
How do I fix frequent account lockout issues?
Troubleshooting steps:
- Click Start, click Run, type “control userpasswords2” (without the quotation marks), and then click OK.
- Click the Advanced tab.
- Click the “Manage Password” button.
- Check to see if these domain account’s passwords are cached. If so, remove them.
- Check if the problem has been resolved now.
How do you fix referenced account is currently locked out?
How to Fix ‘The referenced account is currently locked out’ Issue
- Simply Wait for 30 Minutes.
- Remove the Network Cable.
- Enter BIOS to Change Date and Time.
- Update Local Group Policy Editor.
- Set the Account Password to Never Expires.
- Remove Cached Credentials from your PC.
- Update Group Policy of Windows.
- Check DNS Settings.
How long is an account locked out?
The Account lockout duration policy setting determines the number of minutes that a locked-out account remains locked out before automatically becoming unlocked. The available range is from 1 through 99,999 minutes. A value of 0 specifies that the account will be locked out until an administrator explicitly unlocks it.
How do I find out what is causing my account lockout?
How to: Identify the source of Account Lockouts in Active Directory
- Step 1: Search the domain controller possessing the PDC Emulator Role.
- Step 2: Search for Event ID 4740.
- Step 3: Apply appropriate filters.
- Step 4: Find the locked out user event report from the log.
How do you find out why account is getting locked out?
To find first, once account is locked out, go to Primary Domain controller of your domain and look for Event id 644 in security log, which will give the name of caller machine name. Note down the machine name and time at which event was generated.
How do you troubleshoot account lockouts?
How to: Trace the source of a bad password and account lockout in AD
- Step 1: Download the Account Lockout Status tools from Microsoft.
- Step 2: Run ‘LockoutStatus.exe’
- Step 3: Choose ‘Select Target’ from the File menu.
- Step 4: Check the results.
- Step 5: Check the Security log on one of these DCs.
Why did my Microsoft account get locked?
Your Microsoft account can become locked if there’s a security issue or you enter an incorrect password too many times. Microsoft will send a unique security code to the number. Once you’ve got the code, enter it into the form on the webpage to unlock your account. You’ll now need to change your password.
Why is my Account Locked Out every morning?
This person is a verified professional. Verify your account to enable IT peers to see that you are a professional. The Conficker virus does that sometimes. This usually happens when a password is changed and it had previously been added in somewhere which repeatedly tries to reconnect in some way.
What is the event ID for windows locked out?
Windows event ID 4740 – A user account was locked out. Windows lets you set an account lockout threshold to define the number of times a user can attempt to log on with an invalid password before their account is locked. You can also define the amount of time an account stays locked out with the account lockout duration setting.
What is the name of an Account Locked Out?
Account Name: The name of the account that performed the lockout operation. Account Domain: The domain or computer name. Formats could vary to include the NETBIOS name, the lowercase full domain name, or the uppercase full domain name.
Where can I find the event of locking a domain account?
The event of locking a domain account can be found in the Security log ( Event Viewer -> Windows Logs) on the domain controller. Right click Security item and select Filter Current Log. Filter the security log by event with Event ID 4740.