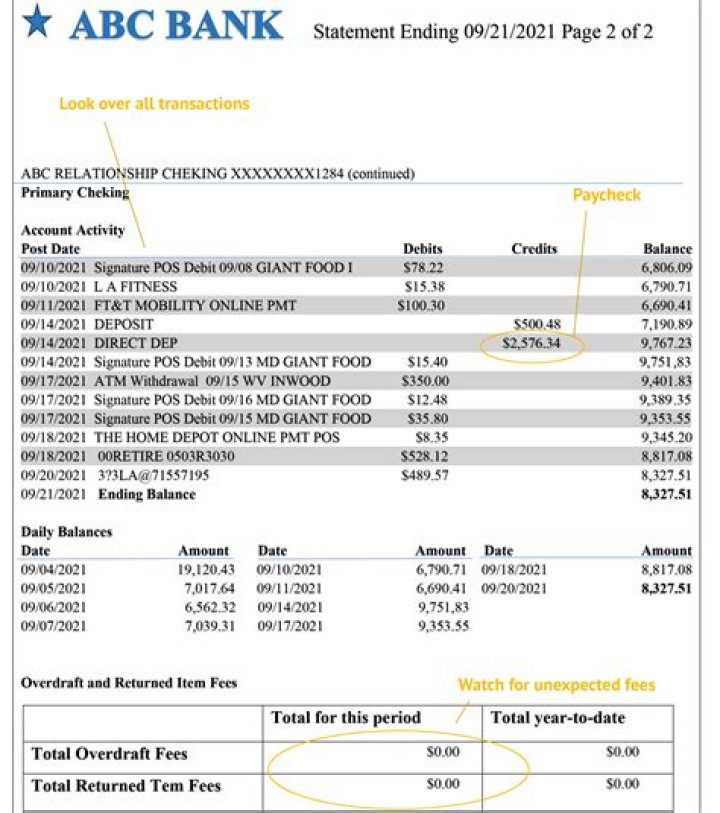
Which of the following is the most common form of authentication?
 Isabella Wilson
Isabella Wilson 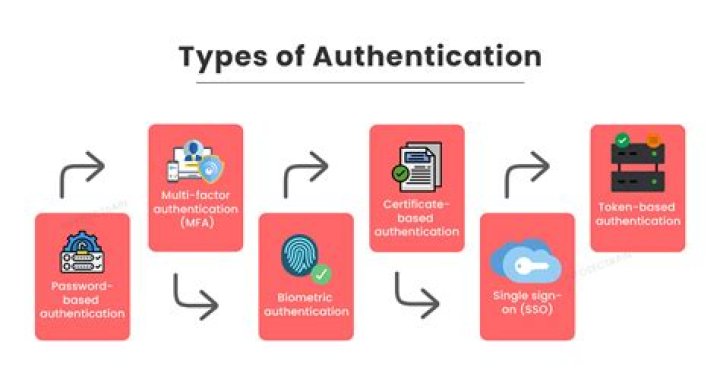
Passwords are the most common form of authentication.
What protocols provide authentication and encryption and is used by most servers for secure exchanges over the Internet?
SSL Stands for secure sockets layer. Protocol for web browsers and servers that allows for the authentication, encryption and decryption of data sent over the Internet.
Why are firewalls considered the first line of defense against LAN security breaches?
Why are firewalls considered the first line of defense against LAN security breaches? Because they provide data confidentiality. The process of verifying the identity of a user who logs on to a system, or the integrity of transmitted data.
What is the most secure method for sending information over the Internet?
Use a VPN. A virtual private network (VPN) will give you a secure tunnel through which you can send and receive information online, as if you were operating using a private server.
What are the 4 general forms of authentication?
Four-factor authentication (4FA) is the use of four types of identity-confirming credentials, typically categorized as knowledge, possession, inherence and location factors.
What does a URL that begins with https signify?
If you see https, the session between the web server and the browser on the mobile device you are using is encrypted. You can easily identify web servers that have https configured by looking at the Uniform Resource Locator (URL) in the web address bar of your browser.
When your companys private LAN is protected by a firewall which of the following is true?
When your company’s private LAN is protected by a firewall, which of the following is true? Users on the LAN can access information from the Internet, but outside users cannot access information stored on the LAN.
What is the first line of defense against a cyber attack?
The visibility and traffic filtering that a firewall provides enables an organization to identify and block a large percentage of malicious traffic before it enters the network perimeter and can provide defense in depth.
What is the safest way to send confidential information?
How To Safely Share Sensitive Information
- Send it in pieces.
- Use a secure service.
- Go old school.
- Use a flash drive.
- Change up your passwords.
- Change it up.
- Don’t keep a list.
What information should never be emailed?
Examples of information you should never send via email include: Social Security numbers. Driver’s License numbers. Passport numbers.
What does a URL without HTTPS signify?
If you see https, the session between the web server and the browser on the mobile device you are using is encrypted. You can easily identify web servers that have https configured by looking at the Uniform Resource Locator (URL) in the web address bar of your browser. Most Web browsers support SSL.
Why do web addresses usually contain HTTP or HTTPS at the beginning?
The “secure” term is there for a reason and it does exactly what it means. HTTPS adds an additional layer of security to your online browsing. It achieves this by encrypting, a process of terming into gibberish content such that it can’t be interpreted by anyone snooping or intercepting your surfing activities.
What is authentication and why is it important?
Authentication acts as the first line of defense to allow access to valuable data only to those who are approved by the organization. Many organizations recognize this and utilize Multi-Factor Authentication (MFA) as an extra layer of protection to RADIUS authentication.
What is the most secure type of firewall?
Proxy Firewalls (Application-Level Gateways) As the most powerfully secure choice available, proxy firewalls serve as an intermediary where source computers connect to the proxy instead of the destination device.
What is the 1st 2nd and 3rd line of defense?
In the Three Lines of Defense model, management control is the first line of defense in risk management, the various risk control and compliance over- sight functions established by management are the second line of defense, and independent assurance is the third.